6 Solutions Teams Evaluate Instead of Teleport for Identity-Aware Access
Identity-aware access has become the new front door to modern infrastructure. Companies want secure logins. They want device checks. They want strong authentication without slowing everyone down. Teleport is a popular choice for this. But it is not the only one. In fact, many teams explore other options before making a final call.
TLDR: Teleport is powerful, but it is not your only choice for identity-aware access. Teams often compare it with tools like Okta, JumpCloud, Cloudflare Access, Tailscale, Zscaler, and Microsoft Entra ID. Each tool has strengths in areas like ease of setup, cost, integrations, and scalability. The best solution depends on your team size, infrastructure, and security goals.
Let’s explore six strong alternatives. We will keep it simple. No jargon overload. Just clear explanations and practical tips.
1. Okta
Table of Contents
Okta is a big name in identity management. Many enterprises trust it. It focuses on single sign-on (SSO), multi-factor authentication (MFA), and lifecycle management.
It works well when:
- You have many SaaS apps.
- You want strong user lifecycle automation.
- You need advanced compliance support.
Okta shines in large organizations. It connects to thousands of applications. That is huge. Your employees log in once. They get access to what they need. Simple.
However, it can get expensive. Smaller teams sometimes feel the pricing pressure.

Why teams evaluate it:
- Strong integrations.
- Mature ecosystem.
- Trusted enterprise security features.
2. JumpCloud
JumpCloud is like a directory-as-a-service platform. It combines identity, device management, and access control.
This is great for:
- Distributed teams.
- Hybrid environments.
- Startups scaling quickly.
JumpCloud allows you to manage:
- Users.
- Devices.
- Servers.
All from one dashboard.
That is powerful. Especially if you do not want to run your own Active Directory.
Key benefits:
- Cloud-based directory.
- Easy device onboarding.
- Cross-platform support (Windows, Mac, Linux).
Some teams choose JumpCloud instead of Teleport when device management is equally important as access control.
3. Cloudflare Access
Cloudflare Access is part of Cloudflare Zero Trust. It protects internal applications. No VPN required.
That sounds good already.
It works by putting an identity layer in front of your apps. Users must verify identity before access is granted.
No traditional network perimeter needed.
This makes it very attractive to:
- Remote-first companies.
- Teams moving away from VPNs.
- Businesses already using Cloudflare services.
Why consider Cloudflare Access?
- Fast deployment.
- Global network performance.
- Strong Zero Trust focus.
However, it focuses more on web apps than deep infrastructure access like SSH and Kubernetes. That distinction matters.
4. Tailscale
Tailscale is simple. Almost shockingly simple.
It builds a secure mesh network using WireGuard. Devices connect directly. Access is based on identity.
Engineers love it because:
- Setup takes minutes.
- No complex firewall rules.
- Works across clouds and on-prem.
You log in with your identity provider. Done. Your device becomes part of the secure network.
This feels magical compared to old-school VPN setups.
Best for:
- Small to mid-size engineering teams.
- DevOps teams managing multi-cloud systems.
- Companies that want minimal overhead.
But it may lack some advanced auditing and compliance features that large enterprises demand.
5. Zscaler Private Access (ZPA)
Zscaler Private Access is a strong Zero Trust Network Access (ZTNA) solution.
It replaces VPNs with identity-based access. Users connect only to specific apps. Not the whole network.
This limits attack surface. Big win.
It stands out because:
- Scales globally.
- Provides detailed policy controls.
- Offers strong threat protection layers.
Large enterprises often compare Zscaler with Teleport when evaluating Zero Trust transformation projects.
But Zscaler focuses more on application access than deep infrastructure management like SSH certificate authorities.
6. Microsoft Entra ID
Formerly known as Azure Active Directory.
Microsoft Entra ID is powerful. Especially for Microsoft-heavy environments.
If your stack includes:
- Azure.
- Microsoft 365.
- Windows endpoints.
Then Entra feels natural.
It supports:
- Conditional access policies.
- Identity governance.
- Privileged identity management.
Enterprises like its deep integration with the Microsoft ecosystem.

However, multi-cloud teams sometimes find it less flexible outside Microsoft infrastructure.
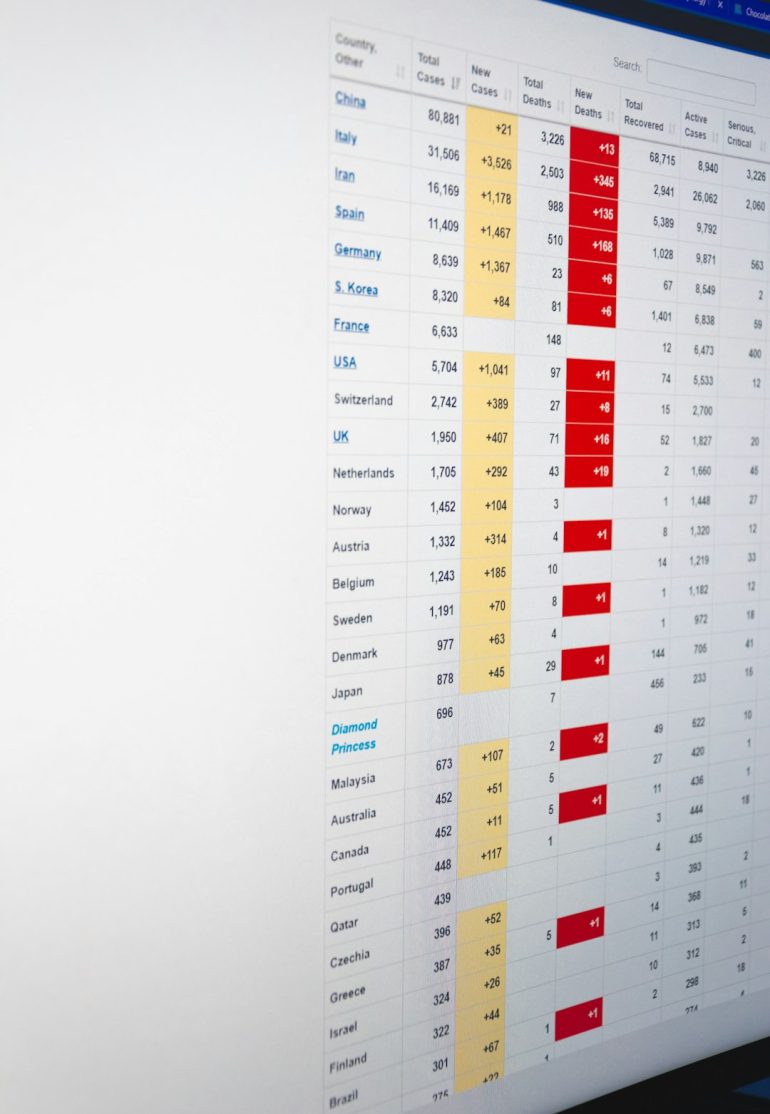
Quick Comparison Chart
| Tool | Best For | Main Strength | Complexity | Enterprise Ready? |
|---|---|---|---|---|
| Okta | Large SaaS-heavy orgs | SSO and lifecycle management | Medium | Yes |
| JumpCloud | Hybrid and distributed teams | Directory plus device management | Medium | Yes |
| Cloudflare Access | Remote web app access | Zero Trust web security | Low to Medium | Yes |
| Tailscale | Engineering teams | Simple identity based networking | Low | Growing |
| Zscaler ZPA | Global enterprises | Scalable Zero Trust architecture | High | Yes |
| Microsoft Entra ID | Microsoft ecosystems | Deep Azure integration | Medium to High | Yes |
How Teams Actually Choose
Here is the truth.
Most teams do not just compare features. They compare fit.
They ask questions like:
- What infrastructure do we already use?
- How technical is our team?
- Do we need compliance certifications?
- How fast do we need to deploy?
- What is our budget?
A startup with 15 engineers will choose differently than a global bank.
That is normal.
Teleport vs The Alternatives
Teleport is especially strong in:
- SSH access control.
- Kubernetes access.
- Certificate-based authentication.
- Infrastructure auditing.
So if deep infrastructure access is your focus, Teleport is hard to beat.
But if your primary need is SaaS app SSO? Okta might win.
If you hate VPN headaches? Tailscale or Cloudflare could be better.
If you live inside Azure? Entra makes more sense.
Different tools solve different pain points.
Final Thoughts
Identity-aware access is not optional anymore. It is essential.
Cyber threats are smarter. Teams are more distributed. Infrastructure is no longer inside one building.
Teleport is a strong solution. But it is part of a bigger ecosystem. Smart teams evaluate multiple options before committing.
The good news?
All six solutions listed here are solid. Mature. Trusted.
The key is alignment.
Match the tool to your infrastructure. Match the complexity to your team. Match the cost to your growth stage.
Do that, and your identity-aware access strategy will not just be secure.
It will be future-ready.